312-50v11 Exam Questions - Online Test
312-50v11 Premium VCE File

150 Lectures, 20 Hours

Act now and download your EC-Council 312-50v11 test today! Do not waste time for the worthless EC-Council 312-50v11 tutorials. Download Down to date EC-Council Certified Ethical Hacker Exam (CEH v11) exam with real questions and answers and begin to learn EC-Council 312-50v11 with a classic professional.
Online EC-Council 312-50v11 free dumps demo Below:
NEW QUESTION 1
The network in ABC company is using the network address 192.168.1.64 with mask 255.255.255.192. In the network the servers are in the addresses 192.168.1.122, 192.168.1.123 and 192.168.1.124. An attacker is trying to find those servers but he cannot see them in his scanning. The command he is using is: nmap 192.168.1.64/28.
Why he cannot see the servers?
- A. He needs to add the command ““ip address”” just before the IP address
- B. He needs to change the address to 192.168.1.0 with the same mask
- C. He is scanning from 192.168.1.64 to 192.168.1.78 because of the mask /28 and the servers are not in that range
- D. The network must be dawn and the nmap command and IP address are ok
Answer: C
NEW QUESTION 2
What is the purpose of a demilitarized zone on a network?
- A. To scan all traffic coming through the DMZ to the internal network
- B. To only provide direct access to the nodes within the DMZ and protect the network behind it
- C. To provide a place to put the honeypot
- D. To contain the network devices you wish to protect
Answer: B
NEW QUESTION 3
Gregory, a professional penetration tester working at Sys Security Ltd., is tasked with performing a security test of web applications used in the company. For this purpose, Gregory uses a tool to test for any security loopholes by hijacking a session between a client and server. This tool has a feature of intercepting proxy that can be used to inspect and modify the traffic between the browser and target application. This tool can also perform customized attacks and can be used to test the randomness of session tokens. Which of the following tools is used by Gregory in the above scenario?
- A. Nmap
- B. Burp Suite
- C. CxSAST
- D. Wireshark
Answer: B
NEW QUESTION 4
John, a security analyst working for an organization, found a critical vulnerability on the organization's LAN that allows him to view financial and personal information about the rest of the employees. Before reporting the vulnerability, he examines the information shown by the vulnerability for two days without disclosing any information to third parties or other internal employees. He does so out of curiosity about the other employees and may take advantage of this information later. What would John be considered as?
- A. Cybercriminal
- B. Black hat
- C. White hat
- D. Gray hat
Answer: D
NEW QUESTION 5
Gerard, a disgruntled ex-employee of Sunglass IT Solutions, targets this organization to perform sophisticated attacks and bring down its reputation in the market. To launch the attacks process, he performed DNS footprinting to gather information about ONS servers and to identify the hosts connected in the target network. He used an automated tool that can retrieve information about DNS zone data including DNS domain names, computer names. IP addresses. DNS records, and network Who is records. He further exploited this information to launch other sophisticated attacks. What is the tool employed by Gerard in the above scenario?
- A. Knative
- B. zANTI
- C. Towelroot
- D. Bluto
Answer: D
Explanation:
https://www.darknet.org.uk/2017/07/bluto-dns-recon-zone-transfer-brute-forcer/
"Attackers also use DNS lookup tools such as DNSdumpster.com, Bluto, and Domain Dossier to retrieve DNS records for a specified domain or hostname. These tools retrieve information such as domains and IP addresses, domain Whois records, DNS records, and network Whois records." CEH Module 02 Page 138
NEW QUESTION 6
You have successfully comprised a server having an IP address of 10.10.0.5. You would like to enumerate all machines in the same network quickly.
What is the best Nmap command you will use?
- A. nmap -T4 -q 10.10.0.0/24
- B. nmap -T4 -F 10.10.0.0/24
- C. nmap -T4 -r 10.10.1.0/24
- D. nmap -T4 -O 10.10.0.0/24
Answer: B
NEW QUESTION 7
You are a penetration tester tasked with testing the wireless network of your client Brakeme SA. You are attempting to break into the wireless network with the SSID "Brakeme-lnternal." You realize that this network uses WPA3 encryption, which of the following vulnerabilities is the promising to exploit?
- A. Dragonblood
- B. Cross-site request forgery
- C. Key reinstallation attack
- D. AP Myconfiguration
Answer: A
Explanation:
Dragonblood allows an attacker in range of a password-protected Wi-Fi network to get the password and gain access to sensitive information like user credentials, emails and mastercard numbers. consistent with the published report:“The WPA3 certification aims to secure Wi-Fi networks, and provides several advantages over its predecessor WPA2, like protection against offline dictionary attacks and forward secrecy. Unfortunately, we show that WPA3 is suffering from several design flaws, and analyze these flaws both theoretically and practically. Most prominently, we show that WPA3’s Simultaneous Authentication of Equals (SAE) handshake, commonly referred to as Dragonfly, is suffering from password partitioning attacks.”Our Wi-Fi researchers at WatchGuard are educating businesses globally that WPA3 alone won’t stop the Wi-Fi hacks that allow attackers to steal information over the air (learn more in our recent blog post on the topic). These Dragonblood vulnerabilities impact alittle amount of devices that were released with WPA3 support, and makers are currently making patches available. one among the most important takeaways for businesses of all sizes is to know that a long-term fix might not be technically feasible for devices with lightweight processing capabilities like IoT and embedded systems. Businesses got to consider adding products that enable a Trusted Wireless Environment for all kinds of devices and users alike.Recognizing that vulnerabilities like KRACK and Dragonblood require attackers to initiate these attacks by bringing an “Evil Twin” Access Point or a Rogue Access Point into a Wi-Fi environment, we’ve been that specialize in developing Wi-Fi security solutions that neutralize these threats in order that these attacks can never occur. The Trusted Wireless Environment framework protects against the “Evil Twin” Access Point and Rogue Access Point. one among these hacks is required to initiate the 2 downgrade or side-channel attacks referenced in Dragonblood.What’s next? WPA3 is an improvement over WPA2 Wi-Fi encryption protocol, however, as we predicted, it still doesn’t provide protection from the six known Wi-Fi threat categories. It’s highly likely that we’ll see more WPA3 vulnerabilities announced within the near future.To help reduce Wi-Fi vulnerabilities, we’re asking all of you to hitch the Trusted Wireless Environment movement and advocate for a worldwide security standard for Wi-Fi.
NEW QUESTION 8
Based on the below log, which of the following sentences are true?
Mar 1, 2016, 7:33:28 AM 10.240.250.23 - 54373 10.249.253.15 - 22 tcp_ip
- A. Application is FTP and 10.240.250.23 is the client and 10.249.253.15 is the server.
- B. Application is SSH and 10.240.250.23 is the server and 10.249.253.15 is the client.
- C. SSH communications are encrypted; it’s impossible to know who is the client or the server.
- D. Application is SSH and 10.240.250.23 is the client and 10.249.253.15 is the server.
Answer: D
NEW QUESTION 9
Garry is a network administrator in an organization. He uses SNMP to manage networked devices from a remote location. To manage nodes in the network, he uses MIB. which contains formal descriptions of all network objects managed by SNMP. He accesses the contents of MIB by using a web browser either by entering the IP address and Lseries.mlb or by entering the DNS library name and Lseries.mlb. He is currently retrieving information from an MIB that contains object types for workstations and server services. Which of the following types of MIB is accessed by Garry in the above scenario?
- A. LNMIB2.MIB
- B. WINS.MIB
- C. DHCP.MIS
- D. MIB_II.MIB
Answer: A
Explanation:
DHCP.MIB: Monitors network traffic between DHCP servers and remote hosts HOSTMIB.MIB: Monitors and manages host resources
LNMIB2.MIB: Contains object types for workstation and server services MIBJI.MIB: Manages TCP/IP-based Internet using a simple architecture and system WINS.MIB: For the Windows Internet Name Service (WINS)
NEW QUESTION 10
This is an attack that takes advantage of a web site vulnerability in which the site displays content that includes un-sanitized user-provided data.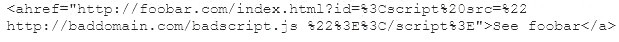
What is this attack?
- A. Cross-site-scripting attack
- B. SQL Injection
- C. URL Traversal attack
- D. Buffer Overflow attack
Answer: A
NEW QUESTION 11
The configuration allows a wired or wireless network interface controller to pass all traffic it receives to the Central Processing Unit (CPU), rather than passing only the frames that the controller is intended to receive. Which of the following is being described?
- A. Multi-cast mode
- B. Promiscuous mode
- C. WEM
- D. Port forwarding
Answer: B
NEW QUESTION 12
______ is a tool that can hide processes from the process list, can hide files, registry entries, and intercept keystrokes.
- A. Trojan
- B. RootKit
- C. DoS tool
- D. Scanner
- E. Backdoor
Answer: B
NEW QUESTION 13
Taylor, a security professional, uses a tool to monitor her company's website, analyze the website's traffic, and track the geographical location of the users visiting the company's website. Which of the following tools did Taylor employ in the above scenario?
- A. WebSite Watcher
- B. web-Stat
- C. Webroot
- D. WAFW00F
Answer: B
Explanation:
Increase your web site’s performance and grow! Add Web-Stat to your site (it’s free!) and watch individuals act together with your pages in real time.
Learn how individuals realize your web site. Get details concerning every visitor’s path through your web site and track pages that flip browsers into consumers.
One-click install. observe locations, in operation systems, browsers and screen sizes and obtain alerts for new guests and conversions
NEW QUESTION 14
When analyzing the IDS logs, the system administrator noticed an alert was logged when the external router was accessed from the administrator’s Computer to update the router configuration. What type of an alert is this?
- A. False negative
- B. True negative
- C. True positive
- D. False positive
Answer: D
Explanation:
True Positive - IDS referring a behavior as an attack, in real life it is
True Negative - IDS referring a behavior not an attack and in real life it is not False Positive - IDS referring a behavior as an attack, in real life it is not
False Negative - IDS referring a behavior not an attack, but in real life is an attack.
False Negative - is the most serious and dangerous state of all !!!!
NEW QUESTION 15
Bob is doing a password assessment for one of his clients. Bob suspects that security policies are not in place. He also suspects that weak passwords are probably the norm throughout the company he is evaluating. Bob is familiar with password weaknesses and key loggers.
Which of the following options best represents the means that Bob can adopt to retrieve passwords from his clients hosts and servers?
- A. Hardware, Software, and Sniffing.
- B. Hardware and Software Keyloggers.
- C. Passwords are always best obtained using Hardware key loggers.
- D. Software only, they are the most effective.
Answer: A
NEW QUESTION 16
......
Thanks for reading the newest 312-50v11 exam dumps! We recommend you to try the PREMIUM Thedumpscentre.com 312-50v11 dumps in VCE and PDF here: https://www.thedumpscentre.com/312-50v11-dumps/ (528 Q&As Dumps)
- Improve Certified Ethical Hacker Exam (CEHv12) 312-50v12 Exam Prep
- Real 412-79v10 Braindumps 2021
- [2021-New] EC-Council 312-50 Dumps With Update Exam Questions (171-180)
- A Review Of Pinpoint 312-50v11 Braindump
- [2021-New] EC-Council 312-50v9 Dumps With Update Exam Questions (21-30)
- [2021-New] EC-Council 312-50v9 Dumps With Update Exam Questions (1-10)
- [2021-New] EC-Council 312-50 Dumps With Update Exam Questions (321-330)
- The Most Recent Guide To 312-49v9 Actual Test
- [2021-New] EC-Council 312-50 Dumps With Update Exam Questions (311-320)
- [2021-New] EC-Council 312-50 Dumps With Update Exam Questions (341-350)

