312-50v12 Exam Questions - Online Test
312-50v12 Premium VCE File

150 Lectures, 20 Hours

Proper study guides for Renewal EC-Council Certified Ethical Hacker Exam (CEHv12) certified begins with EC-Council 312-50v12 preparation products which designed to deliver the Simulation 312-50v12 questions by making you pass the 312-50v12 test at your first time. Try the free 312-50v12 demo right now.
Free 312-50v12 Demo Online For EC-Council Certifitcation:
NEW QUESTION 1
Shiela is an information security analyst working at HiTech Security Solutions. She is performing service version discovery using Nmap to obtain information about the running services and their versions on a target system.
Which of the following Nmap options must she use to perform service version discovery on the target host?
- A. -SN
- B. -SX
- C. -sV
- D. -SF
Answer: C
NEW QUESTION 2
Which type of security feature stops vehicles from crashing through the doors of a building?
- A. Bollards
- B. Receptionist
- C. Mantrap
- D. Turnstile
Answer: A
NEW QUESTION 3
What is GINA?
- A. Gateway Interface Network Application
- B. GUI Installed Network Application CLASS
- C. Global Internet National Authority (G-USA)
- D. Graphical Identification and Authentication DLL
Answer: D
NEW QUESTION 4
As a securing consultant, what are some of the things you would recommend to a company to ensure DNS security?
- A. Use the same machines for DNS and other applications
- B. Harden DNS servers
- C. Use split-horizon operation for DNS servers
- D. Restrict Zone transfers
- E. Have subnet diversity between DNS servers
Answer: BCDE
NEW QUESTION 5
Eve is spending her day scanning the library computers. She notices that Alice is using a computer whose port 445 is active and listening. Eve uses the ENUM tool to enumerate Alice machine. From the command prompt, she types the following command.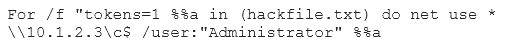
What is Eve trying to do?
- A. Eve is trying to connect as a user with Administrator privileges
- B. Eve is trying to enumerate all users with Administrative privileges
- C. Eve is trying to carry out a password crack for user Administrator
- D. Eve is trying to escalate privilege of the null user to that of Administrator
Answer: C
NEW QUESTION 6
A large company intends to use Blackberry for corporate mobile phones and a security analyst is assigned to evaluate the possible threats. The analyst will use the Blackjacking attack method to demonstrate how an attacker could circumvent perimeter defenses and gain access to the Prometric Online Testing – Reports https://ibt1.prometric.com/users/custom/report_queue/rq_str... corporate network. What tool should the analyst use to perform a Blackjacking attack?
- A. Paros Proxy
- B. BBProxy
- C. Blooover
- D. BBCrack
Answer: B
NEW QUESTION 7
Taylor, a security professional, uses a tool to monitor her company's website, analyze the website's traffic, and track the geographical location of the users visiting the company's website. Which of the following tools did Taylor employ in the above scenario?
- A. WebSite Watcher
- B. web-Stat
- C. Webroot
- D. WAFW00F
Answer: B
Explanation:
Increase your web site’s performance and grow! Add Web-Stat to your site (it’s free!) and watch individuals act together with your pages in real time.
Learn how individuals realize your web site. Get details concerning every visitor’s path through your web site and track pages that flip browsers into consumers.
One-click install. observe locations, in operation systems, browsers and screen sizes and obtain alerts for new guests and conversions
NEW QUESTION 8
which of the following Bluetooth hacking techniques refers to the theft of information from a wireless device through Bluetooth?
- A. Bluesmacking
- B. Bluebugging
- C. Bluejacking
- D. Bluesnarfing
Answer: D
Explanation:
Bluesnarfing is the unauthorized access of information from a wireless device through Ba luetooth
connection, often between phones, desktops, laptops, and PDAs (personal digital assistant).
NEW QUESTION 9
Which of the following web vulnerabilities would an attacker be attempting to exploit if they delivered the following input?
<!DOCTYPE blah [ < IENTITY trustme SYSTEM "file:///etc/passwd" > ] >
- A. XXE
- B. SQLi
- C. IDOR
- D. XXS
Answer: A
NEW QUESTION 10
Tess King is using the nslookup command to craft queries to list all DNS information (such as Name Servers, host names, MX records, CNAME records, glue records (delegation for child Domains), zone serial number, TimeToLive (TTL) records, etc) for a Domain.
What do you think Tess King is trying to accomplish? Select the best answer.
- A. A zone harvesting
- B. A zone transfer
- C. A zone update
- D. A zone estimate
Answer: B
NEW QUESTION 11
When a security analyst prepares for the formal security assessment - what of the following should be done in order to determine inconsistencies in the secure assets database and verify that system is compliant to the minimum security baseline?
- A. Data items and vulnerability scanning
- B. Interviewing employees and network engineers
- C. Reviewing the firewalls configuration
- D. Source code review
Answer: A
NEW QUESTION 12
A security analyst is performing an audit on the network to determine if there are any deviations from the security policies in place. The analyst discovers that a user from the IT department had a dial-out modem installed.
Which security policy must the security analyst check to see if dial-out modems are allowed?
- A. Firewall-management policy
- B. Acceptable-use policy
- C. Permissive policy
- D. Remote-access policy
Answer: D
NEW QUESTION 13
Which among the following is the best example of the hacking concept called "clearing tracks"?
- A. After a system is breached, a hacker creates a backdoor to allow re-entry into a system.
- B. During a cyberattack, a hacker injects a rootkit into a server.
- C. An attacker gains access to a server through an exploitable vulnerability.
- D. During a cyberattack, a hacker corrupts the event logs on all machines.
Answer: D
NEW QUESTION 14
You are logged in as a local admin on a Windows 7 system and you need to launch the Computer Management Console from command line.
Which command would you use?
- A. c:\compmgmt.msc
- B. c:\services.msc
- C. c:\ncpa.cp
- D. c:\gpedit
Answer: A
Explanation:
To start the Computer Management Console from command line just type compmgmt.msc
/computer:computername in your run box or at the command line and it should automatically open the Computer Management console.
References:
http://www.waynezim.com/tag/compmgmtmsc/
NEW QUESTION 15
What kind of detection techniques is being used in antivirus softwares that identifies malware by collecting data from multiple protected systems and instead of analyzing files locally it's made on the premiers environment
- A. VCloud based
- B. Honypot based
- C. Behaviour based
- D. Heuristics based
Answer: A
NEW QUESTION 16
Leverox Solutions hired Arnold, a security professional, for the threat intelligence process. Arnold collected information about specific threats against the organization. From this information, he retrieved contextual information about security events and incidents that helped him disclose potential risks and gain insight into attacker methodologies. He collected the information from sources such as humans, social media, and chat
rooms as well as from events that resulted in cyberattacks. In this process, he also prepared a report that includes identified malicious activities, recommended courses of action, and warnings for emerging attacks. What is the type of threat intelligence collected by Arnold in the above scenario?
- A. Strategic threat intelligence
- B. Tactical threat intelligence
- C. Operational threat intelligence
- D. Technical threat intelligence
Answer: C
NEW QUESTION 17
......
100% Valid and Newest Version 312-50v12 Questions & Answers shared by Dumps-hub.com, Get Full Dumps HERE: https://www.dumps-hub.com/312-50v12-dumps.html (New 572 Q&As)
- [2021-New] EC-Council 312-50 Dumps With Update Exam Questions (311-320)
- High quality 412-79v10 Exam Questions 2021
- [2021-New] EC-Council 312-50 Dumps With Update Exam Questions (191-200)
- [2021-New] EC-Council 312-50 Dumps With Update Exam Questions (111-120)
- A Review Of Pinpoint 312-50v11 Braindump
- [2021-New] EC-Council 312-50v9 Dumps With Update Exam Questions (11-20)
- [2021-New] EC-Council 312-50 Dumps With Update Exam Questions (441-449)
- Far Out 312-50v12 Training Tools For Certified Ethical Hacker Exam (CEHv12) Certification
- [2021-New] EC-Council 312-50 Dumps With Update Exam Questions (1-10)
- All About Simulation 312-50v12 Questions

