350-701 Exam Questions - Online Test
350-701 Premium VCE File

150 Lectures, 20 Hours

Exam Code: 350-701 (Practice Exam Latest Test Questions VCE PDF)
Exam Name: Implementing and Operating Cisco Security Core Technologies
Certification Provider: Cisco
Free Today! Guaranteed Training- Pass 350-701 Exam.
Free demo questions for Cisco 350-701 Exam Dumps Below:
NEW QUESTION 1
What is a difference between Cisco AMP for Endpoints and Cisco Umbrella?
- A. Cisco AMP for Endpoints is a cloud-based service, and Cisco Umbrella is not.
- B. Cisco AMP for Endpoints prevents connections to malicious destinations, and C malware.
- C. Cisco AMP for Endpoints automatically researches indicators of compromise ..
- D. Cisco AMP for Endpoints prevents, detects, and responds to attacks before and against Internet threats.
Answer: D
Explanation:
https://learn-umbrella.cisco.com/i/802005-umbrella-security-report/3? https://www.cisco.com/site/us/en/products/security/endpoint-security/secure-endpoint/index.html#:~:text=Powe Cisco Advanced Malware Protection (AMP) for endpoints can be seen as a replacement for the traditional antivirus solution. It is a next generation, cloud delivered endpoint protection platform (EPP), and advanced endpoint detection and response (EDR). Providing Protection – Detection Response
While Cisco Umbrella can enforce security at the DNS-, IP-, and HTTP/S-layer, this report does not require that blocking is enabled and only monitors your DNS activity. Any malicious domains requested and IPs resolved are indicators of compromise (IOC).
Any malicious domains requested and IPs resolved are indicators of compromise IO( C)
NEW QUESTION 2
What are two functions of TAXII in threat intelligence sharing? (Choose two.)
- A. determines the "what" of threat intelligence
- B. Supports STIX information
- C. allows users to describe threat motivations and abilities
- D. exchanges trusted anomaly intelligence information
- E. determines how threat intelligence information is relayed
Answer: BE
NEW QUESTION 3
Which DoS attack uses fragmented packets in an attempt to crash a target machine?
- A. teardrop
- B. smurf
- C. LAND
- D. SYN flood
Answer: A
Explanation:
Reference: https://www.radware.com/security/ddos-knowledge-center/ddospedia/teardrop-attack/
NEW QUESTION 4
Which SNMPv3 configuration must be used to support the strongest security possible?
- A. asa-host(config)#snmp-server group myv3 v3 privasa-host(config)#snmp-server user andy myv3 auth sha cisco priv des ciscXXXXXXXX asa-host(config)#snmp-server host inside 10.255.254.1 version 3 andy
- B. asa-host(config)#snmp-server group myv3 v3 noauthasa-host(config)#snmp-server user andy myv3 auth sha cisco priv aes 256 ciscXXXXXXXX asa-host(config)#snmp-server host inside 10.255.254.1 version 3 andy
- C. asa-host(config)#snmpserver group myv3 v3 noauthasa-host(config)#snmp-server user andy myv3 auth sha cisco priv 3des ciscXXXXXXXX asa-host(config)#snmp-server host inside 10.255.254.1 version 3 andy
- D. asa-host(config)#snmp-server group myv3 v3 privasa-host(config)#snmp-server user andy myv3 auth sha cisco priv aes 256 ciscXXXXXXXX asa-host(config)#snmp-server host inside 10.255.254.1 version 3 andy
Answer: D
NEW QUESTION 5
Which attack is preventable by Cisco ESA but not by the Cisco WSA?
- A. buffer overflow
- B. DoS
- C. SQL injection
- D. phishing
Answer: D
Explanation:
Reference:
https://www.cisco.com/c/en/us/td/docs/security/esa/esa13-5/user_guide/b_ESA_Admin_Guide_13-5/m_advance
NEW QUESTION 6
An organization is trying to improve their Defense in Depth by blocking malicious destinations prior to a connection being established. The solution must be able to block certain applications from being used within the network. Which product should be used to accomplish this goal?
- A. Cisco Firepower
- B. Cisco Umbrella
- C. ISE
- D. AMP
Answer: B
Explanation:
Cisco Umbrella protects users from accessing malicious domains by proactively analyzing and blocking unsafe destinations – before a connection is ever made. Thus it can protect from phishing attacks by blocking suspicious domains when users click on the given links that an attacker sent.
NEW QUESTION 7
Which technology is used to improve web traffic performance by proxy caching?
- A. WSA
- B. Firepower
- C. FireSIGHT
- D. ASA
Answer: A
NEW QUESTION 8
Which Cisco network security device supports contextual awareness?
- A. Firepower
- B. CISCO ASA
- C. Cisco IOS
- D. ISE
Answer: D
NEW QUESTION 9
Refer to the exhibit.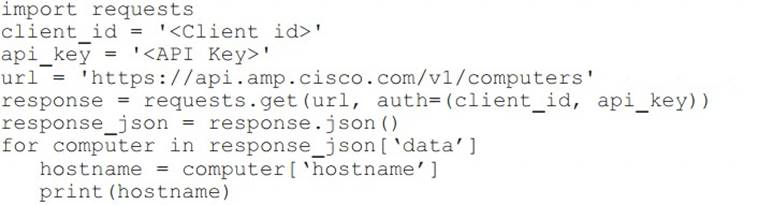
What will happen when the Python script is executed?
- A. The hostname will be translated to an IP address and printed.
- B. The hostname will be printed for the client in the client ID field.
- C. The script will pull all computer hostnames and print them.
- D. The script will translate the IP address to FODN and print it
Answer: C
NEW QUESTION 10
Which type of API is being used when a security application notifies a controller within a software-defined network architecture about a specific security threat?
- A. westbound AP
- B. southbound API
- C. northbound API
- D. eastbound API
Answer: C
NEW QUESTION 11
Drag and drop the capabilities from the left onto the correct technologies on the right.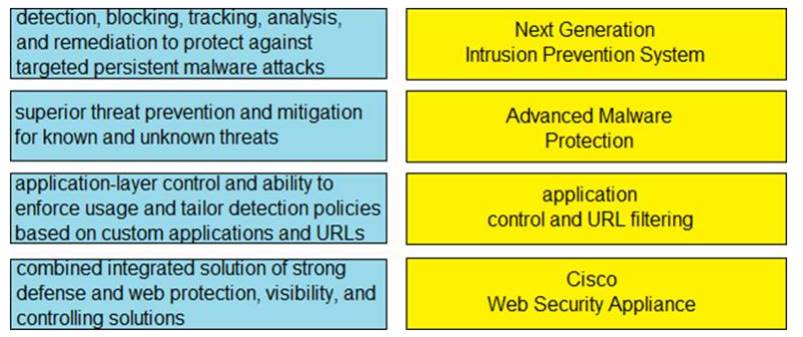
Solution:
Text, chat or text message Description automatically generated
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 12
Why is it important to patch endpoints consistently?
- A. Patching reduces the attack surface of the infrastructure.
- B. Patching helps to mitigate vulnerabilities.
- C. Patching is required per the vendor contract.
- D. Patching allows for creating a honeypot.
Answer: B
NEW QUESTION 13
Which algorithm is an NGE hash function?
- A. HMAC
- B. SHA-1
- C. MD5
- D. SISHA-2
Answer: D
NEW QUESTION 14
An engineer needs a solution for TACACS+ authentication and authorization for device administration. The engineer also wants to enhance wired and wireless network security by requiring users and endpoints to use 802.1X, MAB, or WebAuth. Which product meets all of these requirements?
- A. Cisco Prime Infrastructure
- B. Cisco Identity Services Engine
- C. Cisco Stealthwatch
- D. Cisco AMP for Endpoints
Answer: B
NEW QUESTION 15
Which endpoint solution protects a user from a phishing attack?
- A. Cisco Identity Services Engine
- B. Cisco AnyConnect with ISE Posture module
- C. Cisco AnyConnect with Network Access Manager module
- D. Cisco AnyConnect with Umbrella Roaming Security module
Answer: D
NEW QUESTION 16
In which scenario is endpoint-based security the solution?
- A. inspecting encrypted traffic
- B. device profiling and authorization
- C. performing signature-based application control
- D. inspecting a password-protected archive
Answer: C
NEW QUESTION 17
What is a functional difference between a Cisco ASA and a Cisco IOS router with Zone-based policy firewall?
- A. The Cisco ASA denies all traffic by default whereas the Cisco IOS router with Zone-Based Policy Firewall starts out by allowing all traffic, even on untrusted interfaces
- B. The Cisco IOS router with Zone-Based Policy Firewall can be configured for high availability, whereas the Cisco ASA cannot
- C. The Cisco IOS router with Zone-Based Policy Firewall denies all traffic by default, whereas the Cisco ASA starts out by allowing all traffic until rules are added
- D. The Cisco ASA can be configured for high availability whereas the Cisco IOS router with Zone-Based Policy Firewall cannot
Answer: A
NEW QUESTION 18
Which threat involves software being used to gain unauthorized access to a computer system?
- A. virus
- B. NTP amplification
- C. ping of death
- D. HTTP flood
Answer: A
NEW QUESTION 19
What must be used to share data between multiple security products?
- A. Cisco Rapid Threat Containment
- B. Cisco Platform Exchange Grid
- C. Cisco Advanced Malware Protection
- D. Cisco Stealthwatch Cloud
Answer: B
NEW QUESTION 20
Which function is the primary function of Cisco AMP threat Grid?
- A. automated email encryption
- B. applying a real-time URI blacklist
- C. automated malware analysis
- D. monitoring network traffic
Answer: C
NEW QUESTION 21
......
P.S. Easily pass 350-701 Exam with 631 Q&As Surepassexam Dumps & pdf Version, Welcome to Download the Newest Surepassexam 350-701 Dumps: https://www.surepassexam.com/350-701-exam-dumps.html (631 New Questions)
- [2021-New] Cisco 640-911 Dumps With Update Exam Questions (31-40)
- [2021-New] Cisco 200-355 Dumps With Update Exam Questions (6-15)
- [2021-New] Cisco 200-125 Dumps With Update Exam Questions (1-10)
- [2021-New] Cisco 300-208 Dumps With Update Exam Questions (51-60)
- [2021-New] Cisco 642-997 Dumps With Update Exam Questions (1-10)
- [2021-New] Cisco 200-310 Dumps With Update Exam Questions (1-10)
- [2021-New] Cisco 200-355 Dumps With Update Exam Questions (21-30)
- [2021-New] Cisco 200-310 Dumps With Update Exam Questions (71-80)
- Practical 400-151 Dumps 2021
- [2021-New] Cisco 200-125 Dumps With Update Exam Questions (161-168)

