350-701 Exam Questions - Online Test
350-701 Premium VCE File

150 Lectures, 20 Hours

Our pass rate is high to 98.9% and the similarity percentage between our 350-701 study guide and real exam is 90% based on our seven-year educating experience. Do you want achievements in the Cisco 350-701 exam in just one try? I am currently studying for the Cisco 350-701 exam. Latest Cisco 350-701 Test exam practice questions and answers, Try Cisco 350-701 Brain Dumps First.
Check 350-701 free dumps before getting the full version:
NEW QUESTION 1
Which two capabilities does TAXII support? (Choose two)
- A. Exchange
- B. Pull messaging
- C. Binding
- D. Correlation
- E. Mitigating
Answer: AB
Explanation:
The Trusted Automated eXchangeof Indicator Information (TAXII) specifies mechanisms for exchangingstructured cyber threat information between parties over the network.TAXII exists to provide specific capabilities to those interested in sharing structured cyber threat information.TAXII Capabilities are the highest level at which TAXII actions can be described. There are three capabilitiesthat this version of TAXII supports: push messaging, pull messaging, and discovery.Although there is no “binding” capability in the list but it is the best answer here.
NEW QUESTION 2
Which feature within Cisco ISE verifies the compliance of an endpoint before providing access to the network?
- A. Posture
- B. Profiling
- C. pxGrid
- D. MAB
Answer: A
NEW QUESTION 3
An organization wants to provide visibility and to identify active threats in its network using a VM. The organization wants to extract metadata from network packet flow while ensuring that payloads are not retained or transferred outside the network. Which solution meets these requirements?
- A. Cisco Umbrella Cloud
- B. Cisco Stealthwatch Cloud PNM
- C. Cisco Stealthwatch Cloud PCM
- D. Cisco Umbrella On-Premises
Answer: B
Explanation:
Reference:
https://www.ciscolive.com/c/dam/r/ciscolive/us/docs/2019/pdf/5eU6DfQV/LTRSEC-2240-LG2.pdf
NEW QUESTION 4
An engineer is implementing Cisco CES in an existing Microsoft Office 365 environment and must route inbound email to Cisco CE.. record must be modified to accomplish this task?
- A. CNAME
- B. MX
- C. SPF
- D. DKIM
Answer: B
NEW QUESTION 5
Which action must be taken in the AMP for Endpoints console to detect specific MD5 signatures on endpoints and then quarantine the files?
- A. Configure an advanced custom detection list.
- B. Configure an IP Block & Allow custom detection list
- C. Configure an application custom detection list
- D. Configure a simple custom detection list
Answer: A
NEW QUESTION 6
Which standard is used to automate exchanging cyber threat information?
- A. TAXII
- B. MITRE
- C. IoC
- D. STIX
Answer: A
NEW QUESTION 7
Refer to the exhibit.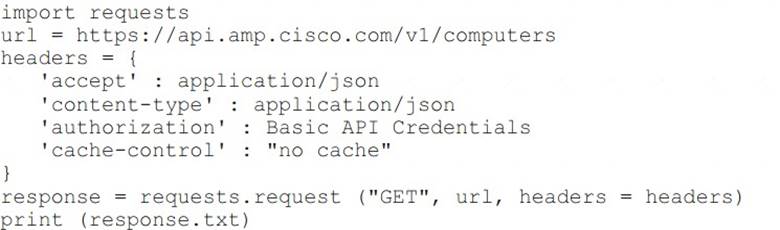
What will happen when this Python script is run?
- A. The compromised computers and malware trajectories will be received from Cisco AMP
- B. The list of computers and their current vulnerabilities will be received from Cisco AMP
- C. The compromised computers and what compromised them will be received from Cisco AMP
- D. The list of computers, policies, and connector statuses will be received from Cisco AMP
Answer: D
Explanation:
Reference:
https://api-docs.amp.cisco.com/api_actions/details?api_action=GET+%2Fv1%2Fcomputers&api_host=api.apjc.
NEW QUESTION 8
An administrator needs to configure the Cisco ASA via ASDM such that the network management system can actively monitor the host using SNMPv3. Which two tasks must be performed for this configuration? (Choose two.)
- A. Specify the SNMP manager and UDP port.
- B. Specify an SNMP user group
- C. Specify a community string.
- D. Add an SNMP USM entry
- E. Add an SNMP host access entry
Answer: BE
NEW QUESTION 9
An organization has two machines hosting web applications. Machine 1 is vulnerable to SQL injection while machine 2 is vulnerable to buffer overflows. What action would allow the attacker to gain access to machine 1 but not machine 2?
- A. sniffing the packets between the two hosts
- B. sending continuous pings
- C. overflowing the buffer’s memory
- D. inserting malicious commands into the database
Answer: D
NEW QUESTION 10
Which Cisco ASA Platform mode disables the threat detection features except for Advanced Threat Statistics?
- A. cluster
- B. transparent
- C. routed
- D. multiple context
Answer: B
NEW QUESTION 11
What is a functional difference between Cisco AMP for Endpoints and Cisco Umbrella Roaming Client?
- A. The Umbrella Roaming client stops and tracks malicious activity on hosts, and AMP for Endpoints tracks only URL-based threats.
- B. The Umbrella Roaming Client authenticates users and provides segmentation, and AMP for Endpoints allows only for VPN connectivity
- C. AMP for Endpoints authenticates users and provides segmentation, and the Umbrella Roaming Client allows only for VPN connectivity.
- D. AMP for Endpoints stops and tracks malicious activity on hosts, and the Umbrella Roaming Client tracks only URL-based threats.
Answer: D
NEW QUESTION 12
Which proxy mode must be used on Cisco WSA to redirect TCP traffic with WCCP?
- A. transparent
- B. redirection
- C. forward
- D. proxy gateway
Answer: A
Explanation:
Reference: https://www.cisco.com/c/dam/en/us/td/docs/solutions/CVD/Aug2013/CVDWebSecurityUsingCiscoWSADesign
NEW QUESTION 13
What is a feature of container orchestration?
- A. ability to deploy Amazon ECS clusters by using the Cisco Container Platform data plane
- B. ability to deploy Amazon EKS clusters by using the Cisco Container Platform data plane
- C. ability to deploy Kubernetes clusters in air-gapped sites
- D. automated daily updates
Answer: C
NEW QUESTION 14
Which Talos reputation center allows you to track the reputation of IP addresses for email and web traffic?
- A. IP Blacklist Center
- B. File Reputation Center
- C. AMP Reputation Center
- D. IP and Domain Reputation Center
Answer: D
NEW QUESTION 15
What is the benefit of integrating Cisco ISE with a MDM solution?
- A. It provides compliance checks for access to the network
- B. It provides the ability to update other applications on the mobile device
- C. It provides the ability to add applications to the mobile device through Cisco ISE
- D. It provides network device administration access
Answer: A
Explanation:
https://www.cisco.com/c/en/us/td/docs/security/ise/2-4/admin_guide/b_ISE_admin_guide_24/m_ise_interoperab
NEW QUESTION 16
How does Cisco Stealthwatch Cloud provide security for cloud environments?
- A. It delivers visibility and threat detection.
- B. It prevents exfiltration of sensitive data.
- C. It assigns Internet-based DNS protection for clients and servers.
- D. It facilitates secure connectivity between public and private networks.
Answer: A
Explanation:
Cisco Stealthwatch Cloud: Available as an SaaS product offer to provide visibility and threat detection within public cloud infrastructures such as Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP).
NEW QUESTION 17
An engineer is trying to securely connect to a router and wants to prevent insecure algorithms from being used. However, the connection is failing. Which action should be taken to accomplish this goal?
- A. Disable telnet using the no ip telnet command.
- B. Enable the SSH server using the ip ssh server command.
- C. Configure the port using the ip ssh port 22 command.
- D. Generate the RSA key using the crypto key generate rsa command.
Answer: D
Explanation:
In this question, the engineer was trying to secure the connection so maybe he was trying to allow SSH to the device. But maybe something went wrong so the connection was failing (the connection used to be good). So maybe he was missing the “crypto key generate rsa” command.
NEW QUESTION 18
Which portion of the network do EPP solutions solely focus on and EDR solutions do not?
- A. server farm
- B. perimeter
- C. core
- D. East-West gateways
Answer: B
NEW QUESTION 19
What is an advantage of the Cisco Umbrella roaming client?
- A. the ability to see all traffic without requiring TLS decryption
- B. visibility into IP-based threats by tunneling suspicious IP connections
- C. the ability to dynamically categorize traffic to previously uncategorized sites
- D. visibility into traffic that is destined to sites within the office environment
Answer: C
NEW QUESTION 20
Which feature enables a Cisco ISR to use the default bypass list automatically for web filtering?
- A. filters
- B. group key
- C. company key
- D. connector
Answer: D
NEW QUESTION 21
......
P.S. Thedumpscentre.com now are offering 100% pass ensure 350-701 dumps! All 350-701 exam questions have been updated with correct answers: https://www.thedumpscentre.com/350-701-dumps/ (631 New Questions)
- [2021-New] Cisco 300-075 Dumps With Update Exam Questions (91-100)
- [2021-New] Cisco 200-310 Dumps With Update Exam Questions (121-130)
- [2021-New] Cisco 300-320 Dumps With Update Exam Questions (31-40)
- [2021-New] Cisco 200-125 Dumps With Update Exam Questions (15-24)
- [2021-New] Cisco 640-916 Dumps With Update Exam Questions (11-20)
- [2021-New] Cisco 300-320 Dumps With Update Exam Questions (141-150)
- [2021-New] Cisco 210-260 Dumps With Update Exam Questions (1-10)
- [2021-New] Cisco 300-135 Dumps With Update Exam Questions (1-10)
- [2021-New] Cisco 400-051 Dumps With Update Exam Questions (61-70)
- [2021-New] Cisco 640-916 Dumps With Update Exam Questions (71-80)

