350-701 Exam Questions - Online Test
350-701 Premium VCE File

150 Lectures, 20 Hours

Cause all that matters here is passing the Cisco 350-701 exam. Cause all that you need is a high score of 350-701 Implementing and Operating Cisco Security Core Technologies exam. The only one thing you need to do is downloading Ucertify 350-701 exam study guides now. We will not let you down with our money-back guarantee.
Online Cisco 350-701 free dumps demo Below:
NEW QUESTION 1
An organization must add new firewalls to its infrastructure and wants to use Cisco ASA or Cisco FTD.
The chosen firewalls must provide methods of blocking traffic that include offering the user the option to bypass the block for certain sites after displaying a warning page and to reset the connection. Which solution should the organization choose?
- A. Cisco FTD because it supports system rate level traffic blocking, whereas Cisco ASA does not
- B. Cisco ASA because it allows for interactive blocking and blocking with reset to be configured via the GUI, whereas Cisco FTD does not.
- C. Cisco FTD because it enables interactive blocking and blocking with reset natively, whereas Cisco ASAdoes not
- D. Cisco ASA because it has an additional module that can be installed to provide multiple blocking capabilities, whereas Cisco FTD does not.
Answer: C
NEW QUESTION 2
What is provided by the Secure Hash Algorithm in a VPN?
- A. integrity
- B. key exchange
- C. encryption
- D. authentication
Answer: A
Explanation:
Reference: https://www.ciscopress.com/articles/article.asp?p=24833&seqNum=4
NEW QUESTION 3
What is the purpose of the certificate signing request when adding a new certificate for a server?
- A. It is the password for the certificate that is needed to install it with.
- B. It provides the server information so a certificate can be created and signed
- C. It provides the certificate client information so the server can authenticate against it when installing
- D. It is the certificate that will be loaded onto the server
Answer: B
Explanation:
A certificate signing request (CSR) is one of the first steps towards getting your own SSL Certificate. Generated on the same server you plan to install the certificate on, the CSR contains information (e.g. common name, organization, country) that the Certificate Authority (CA) will use to create your certificate. It also contains the public key that will be included in your certificate and is signed with the corresponding private key
NEW QUESTION 4
Which baseline form of telemetry is recommended for network infrastructure devices?
- A. SDNS
- B. NetFlow
- C. passive taps
- D. SNMP
Answer: D
NEW QUESTION 5
Which category includes DoS Attacks?
- A. Virus attacks
- B. Trojan attacks
- C. Flood attacks
- D. Phishing attacks
Answer: C
NEW QUESTION 6
What is a function of Cisco AMP for Endpoints?
- A. It detects DNS attacks
- B. It protects against web-based attacks
- C. It blocks email-based attacks
- D. It automates threat responses of an infected host
Answer: D
NEW QUESTION 7
Email security has become a high priority task for a security engineer at a large multi-national organization due to ongoing phishing campaigns. To help control this, the engineer has deployed an Incoming Content Filter with a URL reputation of (-10 00 to -6 00) on the Cisco ESA Which action will the system perform to disable any links in messages that match the filter?
- A. Defang
- B. Quarantine
- C. FilterAction
- D. ScreenAction
Answer: B
Explanation:
Reference: https://www.cisco.com/c/dam/en/us/products/collateral/security/esa-content-filters.pdf
NEW QUESTION 8
What is the function of the Context Directory Agent?
- A. maintains users’ group memberships
- B. relays user authentication requests from Web Security Appliance to Active Directory
- C. reads the Active Directory logs to map IP addresses to usernames
- D. accepts user authentication requests on behalf of Web Security Appliance for user identification
Answer: C
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/security/ibf/cda_10/Install_Config_guide/cda10/cda_oveviw.html
NEW QUESTION 9
Which network monitoring solution uses streams and pushes operational data to provide a near real-time view of activity?
- A. SNMP
- B. SMTP
- C. syslog
- D. model-driven telemetry
Answer: D
Explanation:
Reference: https://developer.cisco.com/docs/ios-xe/#!streaming-telemetry-quick-start-guide
NEW QUESTION 10
What is the purpose of joining Cisco WSAs to an appliance group?
- A. All WSAs in the group can view file analysis results.
- B. The group supports improved redundancy
- C. It supports cluster operations to expedite the malware analysis process.
- D. It simplifies the task of patching multiple appliances.
Answer: A
NEW QUESTION 11
Which two solutions help combat social engineering and phishing at the endpoint level? (Choose two.)
- A. Cisco Umbrella
- B. Cisco ISE
- C. Cisco DNA Center
- D. Cisco TrustSec
- E. Cisco Duo Security
Answer: AE
NEW QUESTION 12
A Cisco Firepower administrator needs to configure a rule to allow a new application that has never been seen on the network. Which two actions should be selected to allow the traffic to pass without inspection? (Choose
two)
- A. permit
- B. trust
- C. reset
- D. allow
- E. monitor
Answer: BE
Explanation:
Each rule also has an action, which determines whether you monitor, trust, block, or allow matching traffic.Note: With action “trust”, Firepower does not do any more inspection on the traffic. There will be no intrusion protection and also no file-policy on this traffic.
NEW QUESTION 13
A network administrator needs to find out what assets currently exist on the network. Third-party systems need to be able to feed host data into Cisco Firepower. What must be configured to accomplish this?
- A. a Network Discovery policy to receive data from the host
- B. a Threat Intelligence policy to download the data from the host
- C. a File Analysis policy to send file data into Cisco Firepower
- D. a Network Analysis policy to receive NetFlow data from the host
Answer: A
Explanation:
You can configure discovery rules to tailor the discovery of host and application data to your needs.The Firepower System can use data from NetFlow exporters to generate connection and discovery events, and to add host and application data to the network map.A network analysis policy governs how traffic is decoded and preprocessed so it can be further evaluated, especially for anomalous traffic that might signal an intrusion attempt -> Answer D is not correct.
NEW QUESTION 14
An organization recently installed a Cisco WSA and would like to take advantage of the AVC engine to allow the organization to create a policy to control application specific activity. After enabling the AVC engine, what must be done to implement this?
- A. Use security services to configure the traffic monitor, .
- B. Use URL categorization to prevent the application traffic.
- C. Use an access policy group to configure application control settings.
- D. Use web security reporting to validate engine functionality
Answer: C
Explanation:
The Application Visibility and Control (AVC) engine lets you create policies to control application activity on the network without having to fully understand the underlying technology of each application. You can configure application control settings in Access Policy groups. You can block or allow applications individually or according to application type. You can also apply controls to particular application types.
NEW QUESTION 15
Which solution protects hybrid cloud deployment workloads with application visibility and segmentation?
- A. Nexus
- B. Stealthwatch
- C. Firepower
- D. Tetration
Answer: D
NEW QUESTION 16
A network engineer must monitor user and device behavior within the on-premises network. This data must be sent to the Cisco Stealthwatch Cloud analytics platform for analysis. What must be done to meet this
requirement using the Ubuntu-based VM appliance deployed in a VMware-based hypervisor?
- A. Configure a Cisco FMC to send syslogs to Cisco Stealthwatch Cloud
- B. Deploy the Cisco Stealthwatch Cloud PNM sensor that sends data to Cisco Stealthwatch Cloud
- C. Deploy a Cisco FTD sensor to send network events to Cisco Stealthwatch Cloud
- D. Configure a Cisco FMC to send NetFlow to Cisco Stealthwatch Cloud
Answer: B
Explanation:
Reference:
https://www.ciscolive.com/c/dam/r/ciscolive/us/docs/2019/pdf/5eU6DfQV/LTRSEC-2240-LG2.pdf
NEW QUESTION 17
Which feature is used in a push model to allow for session identification, host reauthentication, and session termination?
- A. AAA attributes
- B. CoA request
- C. AV pair
- D. carrier-grade NAT
Answer: C
NEW QUESTION 18
Refer to the exhibit.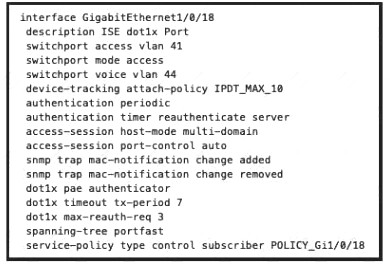
What will occur when this device tries to connect to the port?
- A. 802.1X will not work, but MAB will start and allow the device on the network.
- B. 802.1X will not work and the device will not be allowed network access
- C. 802 1X will work and the device will be allowed on the network
- D. 802 1X and MAB will both be used and ISE can use policy to determine the access level
Answer: B
NEW QUESTION 19
An engineer is adding a Cisco DUO solution to the current TACACS+ deployment using Cisco ISE. The engineer wants to authenticate users using their account when they log into network devices. Which action accomplishes this task?
- A. Configure Cisco DUO with the external Active Directory connector and tie it to the policy set within Cisco ISE.
- B. Install and configure the Cisco DUO Authentication Proxy and configure the identity source sequence within Cisco ISE
- C. Create an identity policy within Cisco ISE to send all authentication requests to Cisco DUO.
- D. Modify the current policy with the condition MFASourceSequence DUO=true in the authorization conditions within Cisco ISE
Answer: B
NEW QUESTION 20
Which form of attack is launched using botnets?
- A. EIDDOS
- B. virus
- C. DDOS
- D. TCP flood
Answer: C
Explanation:
A botnet is a collection of internet-connected devices infected by malware that allow hackers to control them.Cyber criminals use botnets to instigate botnet attacks, which include malicious activities such as credentialsleaks, unauthorized access, data theft and DDoS attacks.
NEW QUESTION 21
......
Recommend!! Get the Full 350-701 dumps in VCE and PDF From Surepassexam, Welcome to Download: https://www.surepassexam.com/350-701-exam-dumps.html (New 631 Q&As Version)
- [2021-New] Cisco 300-115 Dumps With Update Exam Questions (11-20)
- [2021-New] Cisco 200-125 Dumps With Update Exam Questions (4-13)
- [2021-New] Cisco 400-051 Dumps With Update Exam Questions (91-100)
- [2021-New] Cisco 300-070 Dumps With Update Exam Questions (61-70)
- 100% Correct 642-889 Braindumps 2021
- [2021-New] Cisco 642-997 Dumps With Update Exam Questions (11-20)
- Approved 500-651 Free Practice Questions 2021
- [2021-New] Cisco 642-997 Dumps With Update Exam Questions (41-48)
- [2021-New] Cisco 300-208 Dumps With Update Exam Questions (71-80)
- Validated 300-375 Questions 2021

