350-701 Exam Questions - Online Test
350-701 Premium VCE File

150 Lectures, 20 Hours

Exact of 350-701 torrent materials and practice exam for Cisco certification for client, Real Success Guaranteed with Updated 350-701 pdf dumps vce Materials. 100% PASS Implementing and Operating Cisco Security Core Technologies exam Today!
Cisco 350-701 Free Dumps Questions Online, Read and Test Now.
NEW QUESTION 1
What is the function of SDN southbound API protocols?
- A. to allow for the dynamic configuration of control plane applications
- B. to enable the controller to make changes
- C. to enable the controller to use REST
- D. to allow for the static configuration of control plane applications
Answer: B
Explanation:
Reference: https://www.ciscopress.com/articles/article.asp?p=3004581&seqNum=2
Note: Southbound APIs helps us communicate with data plane (not control plane) applications
NEW QUESTION 2
How does Cisco Workload Optimization portion of the network do EPP solutions solely performance issues?
- A. It deploys an AWS Lambda system
- B. It automates resource resizing
- C. It optimizes a flow path
- D. It sets up a workload forensic score
Answer: B
NEW QUESTION 3
Which technology provides a combination of endpoint protection endpoint detection, and response?
- A. Cisco AMP
- B. Cisco Talos
- C. Cisco Threat Grid
- D. Cisco Umbrella
Answer: A
NEW QUESTION 4
What is a benefit of using Cisco Umbrella?
- A. DNS queries are resolved faster.
- B. Attacks can be mitigated before the application connection occurs.
- C. Files are scanned for viruses before they are allowed to run.
- D. It prevents malicious inbound traffic.
Answer: B
NEW QUESTION 5
Which two tasks allow NetFlow on a Cisco ASA 5500 Series firewall? (Choose two)
- A. Enable NetFlow Version 9.
- B. Create an ACL to allow UDP traffic on port 9996.
- C. Apply NetFlow Exporter to the outside interface in the inbound direction.
- D. Create a class map to match interesting traffic.
- E. Define a NetFlow collector by using the flow-export command
Answer: CE
NEW QUESTION 6
Refer to the exhibit.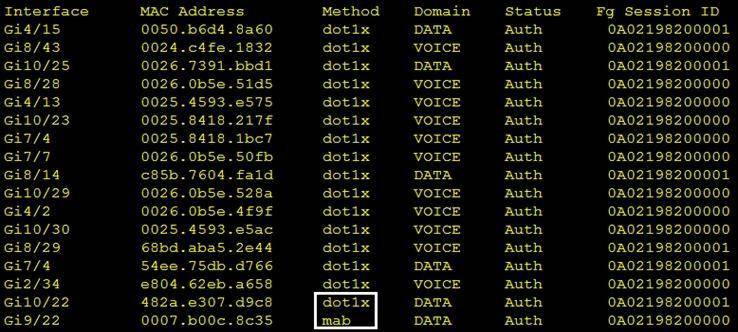
Which command was used to generate this output and to show which ports are authenticating with dot1x or mab?
- A. show authentication registrations
- B. show authentication method
- C. show dot1x all
- D. show authentication sessions
Answer: D
Explanation:
https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/security/s1/sec-s1-xe-3se-3850-cr-book/sec-s1-xe-3se-3850-c Displaying the Summary of All Auth Manager Sessions on the Switch
Enter the following:
Switch# show authentication sessions
Interface MAC Address Method Domain Status Session ID
Gi1/48 0015.63b0.f676 dot1x DATA Authz Success 0A3462B1000000102983C05C Gi1/5 000f.23c4.a401 mab DATA Authz Success 0A3462B10000000D24F80B58
Gi1/5 0014.bf5d.d26d dot1x DATA Authz Success 0A3462B10000000E29811B94
NEW QUESTION 7
Which open standard creates a framework for sharing threat intelligence in a machine-digestible format?
- A. OpenC2
- B. OpenlOC
- C. CybOX
- D. STIX
Answer: D
NEW QUESTION 8
An engineer is deploying Cisco Advanced Malware Protection (AMP) for Endpoints and wants to create a policy that prevents users from executing file named abc424952615.exe without quarantining that file What type of Outbreak Control list must the SHA.-256 hash value for the file be added to in order to accomplish this?
- A. Advanced Custom Detection
- B. Blocked Application
- C. Isolation
- D. Simple Custom Detection
Answer: B
NEW QUESTION 9
An engineer is implementing DHCP security mechanisms and needs the ability to add additional attributes to profiles that are created within Cisco ISE Which action accomplishes this task?
- A. Define MAC-to-lP address mappings in the switch to ensure that rogue devices cannot get an IP address
- B. Use DHCP option 82 to ensure that the request is from a legitimate endpoint and send the information to Cisco ISE
- C. Modify the DHCP relay and point the IP address to Cisco ISE.
- D. Configure DHCP snooping on the switch VLANs and trust the necessary interfaces
Answer: D
NEW QUESTION 10
Why is it important for the organization to have an endpoint patching strategy?
- A. so the organization can identify endpoint vulnerabilities
- B. so the internal PSIRT organization is aware of the latest bugs
- C. so the network administrator is notified when an existing bug is encountered
- D. so the latest security fixes are installed on the endpoints
Answer: D
NEW QUESTION 11
An engineer adds a custom detection policy to a Cisco AMP deployment and encounters issues with the configuration. The simple detection mechanism is configured, but the dashboard indicates that the hash is not 64 characters and is non-zero. What is the issue?
- A. The engineer is attempting to upload a hash created using MD5 instead of SHA-256
- B. The file being uploaded is incompatible with simple detections and must use advanced detections
- C. The hash being uploaded is part of a set in an incorrect format
- D. The engineer is attempting to upload a file instead of a hash
Answer: A
NEW QUESTION 12
Which ESA implementation method segregates inbound and outbound email?
- A. one listener on a single physical Interface
- B. pair of logical listeners on a single physical interface with two unique logical IPv4 addresses and one IPv6 address
- C. pair of logical IPv4 listeners and a pair Of IPv6 listeners on two physically separate interfaces
- D. one listener on one logical IPv4 address on a single logical interface
Answer: D
NEW QUESTION 13
A company is experiencing exfiltration of credit card numbers that are not being stored on-premise. The company needs to be able to protect sensitive data throughout the full environment. Which tool should be used to accomplish this goal?
- A. Security Manager
- B. Cloudlock
- C. Web Security Appliance
- D. Cisco ISE
Answer: B
Explanation:
Cisco Cloudlock is a cloud-native cloud access security broker (CASB) that helps you move to the cloud safely. It protects your cloud users, data, and apps. Cisco Cloudlock provides visibility and compliance checks, protects data against misuse and exfiltration, and provides threat protections against malware like ransomware.
NEW QUESTION 14
Which Cisco Umbrella package supports selective proxy for Inspection of traffic from risky domains?
- A. SIG Advantage
- B. DNS Security Essentials
- C. SIG Essentials
- D. DNS Security Advantage
Answer: C
NEW QUESTION 15
Which policy represents a shared set of features or parameters that define the aspects of a managed device that are likely to be similar to other managed devices in a deployment?
- A. Group Policy
- B. Access Control Policy
- C. Device Management Policy
- D. Platform Service Policy
Answer: D
Explanation:
Reference:
https://www.cisco.com/c/en/us/td/docs/security/firepower/620/configuration/guide/fpmc-configguide-v62/platfo the answer should be “Platform Settings Policy”, not “Platform Service Policy” but it is the bestanswer here so we have to choose it.
NEW QUESTION 16
What are two benefits of Flexible NetFlow records? (Choose two)
- A. They allow the user to configure flow information to perform customized traffic identification
- B. They provide attack prevention by dropping the traffic
- C. They provide accounting and billing enhancements
- D. They converge multiple accounting technologies into one accounting mechanism
- E. They provide monitoring of a wider range of IP packet information from Layer 2 to 4
Answer: AD
Explanation:
Reference: https://www.cisco.com/en/US/docs/ios/fnetflow/configuration/guide/cust_fnflow_rec_mon_external_docbase_0 d9.html#wp1057997Note: Traditional NetFlow allows us to monitor from Layer 2 to 4 but Flexible NetFlow goes beyond theselayers.
NEW QUESTION 17
Which command enables 802.1X globally on a Cisco switch?
- A. dot1x system-auth-control
- B. dot1x pae authenticator
- C. authentication port-control aut
- D. aaa new-model
Answer: A
NEW QUESTION 18
Refer to the exhibit.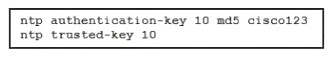
A network engineer is testing NTP authentication and realizes that any device synchronizes time with this router and that NTP authentication is not enforced What is the cause of this issue?
- A. The key was configured in plain text.
- B. NTP authentication is not enabled.
- C. The hashing algorithm that was used was MD5. which is unsupported.
- D. The router was not rebooted after the NTP configuration updated.
Answer: B
NEW QUESTION 19
What is a benefit of using GET VPN over FlexVPN within a VPN deployment?
- A. GET VPN supports Remote Access VPNs
- B. GET VPN natively supports MPLS and private IP networks
- C. GET VPN uses multiple security associations for connections
- D. GET VPN interoperates with non-Cisco devices
Answer: B
NEW QUESTION 20
Refer to the exhibit.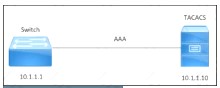
An engineer must configure a Cisco switch to perform PPP authentication via a TACACS server located at IP address 10.1.1.10. Authentication must fall back to the local database using the username LocalUser and password C1Sc0451069341l if the TACACS server is unreachable.
Drag and drop the commands from the left onto the corresponding configuration steps on the right.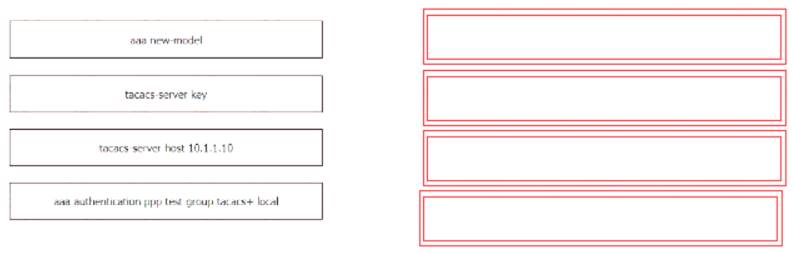
Solution:
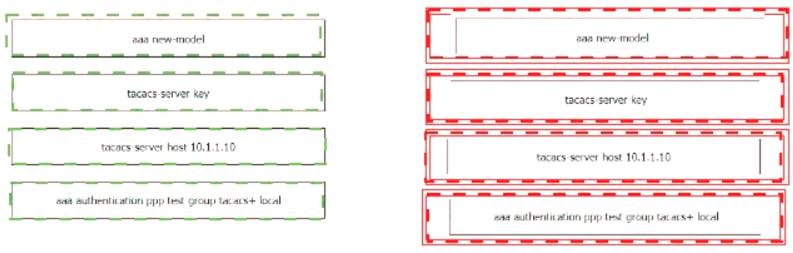
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 21
......
100% Valid and Newest Version 350-701 Questions & Answers shared by Certleader, Get Full Dumps HERE: https://www.certleader.com/350-701-dumps.html (New 631 Q&As)
- Cisco 210-065 Dumps Questions 2021
- The Down To Date Guide To 500-470 Testing Bible
- [2021-New] Cisco 300-207 Dumps With Update Exam Questions (71-80)
- [2021-New] Cisco 200-125 Dumps With Update Exam Questions (7-14)
- [2021-New] Cisco 400-051 Dumps With Update Exam Questions (9-18)
- Most Up-to-date Cisco Certified Network Associate 200-301 Free Practice Exam
- Most Up-to-date 300-165 Forum 2021
- [2021-New] Cisco 210-260 Dumps With Update Exam Questions (31-40)
- [2021-New] Cisco 200-125 Dumps With Update Exam Questions (1-10)
- [2021-New] Cisco 100-105 Dumps With Update Exam Questions (1-10)

