200-301 Exam Questions - Online Test
200-301 Premium VCE File

150 Lectures, 20 Hours

Certleader offers free demo for 200-301 exam. "Cisco Certified Network Associate", also known as 200-301 exam, is a Cisco Certification. This set of posts, Passing the Cisco 200-301 exam, will help you answer those questions. The 200-301 Questions & Answers covers all the knowledge points of the real exam. 100% real Cisco 200-301 exams and revised by experts!
Check 200-301 free dumps before getting the full version:
NEW QUESTION 1
Which two actions are performed by the Weighted Random Early Detection mechanism? (Choose two)
- A. It drops lower-priority packets before it drops higher-priority packets
- B. It can identify different flows with a high level of granularity
- C. It guarantees the delivery of high-priority packets
- D. It can mitigate congestion by preventing the queue from filling up
- E. it supports protocol discovery
Answer: AD
Explanation:
Weighted Random Early Detection (WRED) is just a congestion avoidance mechanism. WRED drops packets selectively based on IP precedence. Edge routers assign IP precedences to packets as they enter the network. When a packet arrives, the following events occur:
* 1. The average queue size is calculated.2. If the average is less than the minimum queue threshold, the arriving packet is queued.3. If the average is between the minimum queue threshold for that type of traffic and the maximum threshold for the interface, the packet is either dropped or queued, depending on the packet drop probability for that type of traffic.4. If the average queue size is greater than the maximum threshold, the packet is dropped. WRED reduces the chances of tail drop (when the queue is full, the packet is dropped) by selectively dropping packets when the output interface begins to show signs of congestion (thus it can mitigate congestion by preventing the queue from filling up). By dropping some packets early rather than waiting until the queue is full, WRED avoids dropping large numbers of packets at once and minimizes the chances of global synchronization. Thus, WRED allows the transmission line to be usedfully at all times.
WRED generally drops packets selectively based on IP precedence. Packets with a higher IP precedence are less likely to be dropped than packets with a lower precedence. Thus, the higher the priority of a packet, the higher the probability that the packet will be delivered
NEW QUESTION 2
Refer to the exhibit.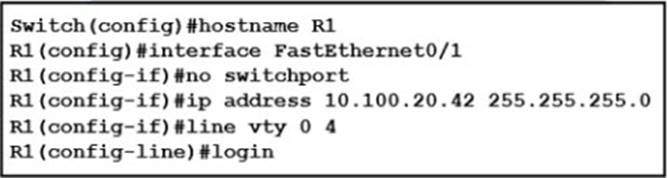
An engineer booted a new switch and applied this configuration via the console port. Which additional configuration must be applied to allow administrators to authenticate directly to enable privilege mode via Telnet using a local username and password?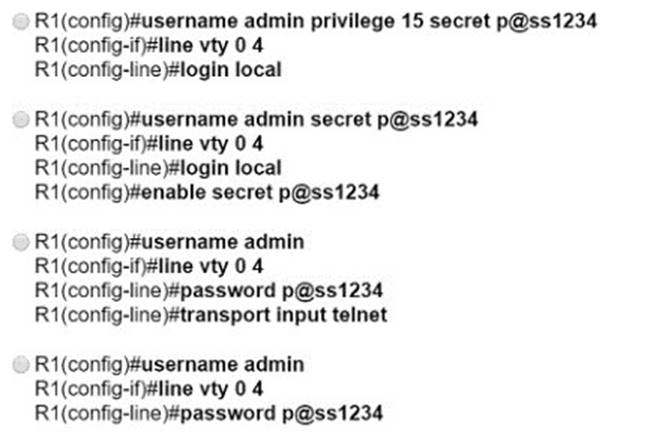
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: A
NEW QUESTION 3
DRAG DROP
Drag and drop the 802.11 wireless standards from the left onto the matching statements on the right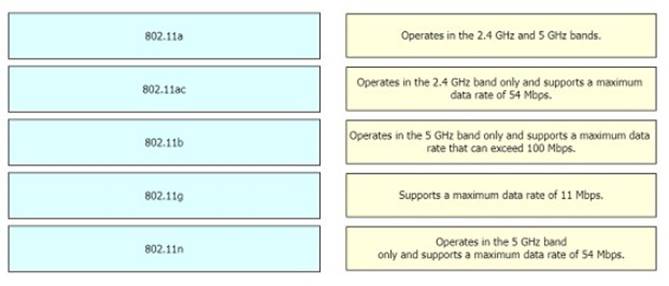
Solution:
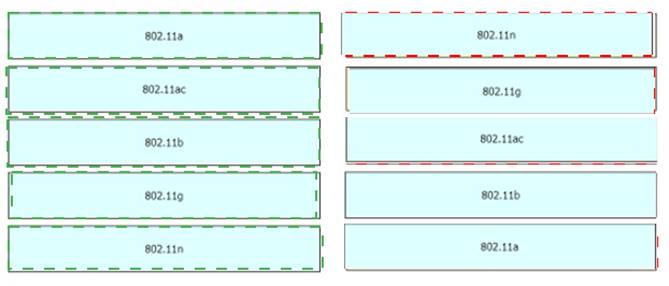
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 4
Which command prevents passwords from being stored in the configuration as plain text on a router or switch?
- A. enable secret
- B. service password-encryption
- C. username Cisco password encrypt
- D. enable password
Answer: B
NEW QUESTION 5
What differentiates device management enabled by cisco DNA center from traditional campus device management?
- A. CLI-oriented device
- B. device-by-device hands-on
- C. centralized
- D. per-device
Answer: C
NEW QUESTION 6
Refer to the exhibit.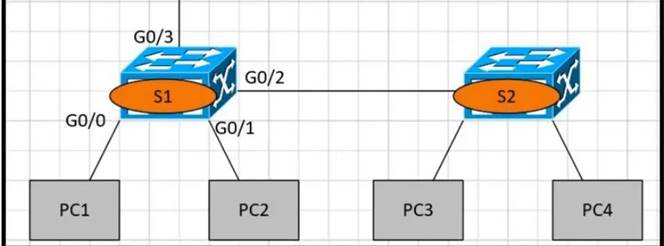
PC1 is trying to ping PC3 for the first time and sends out an ARP to S1 Which action is taken by S1?
- A. It forwards it out G0/3 only
- B. It is flooded out every port except G0/0.
- C. It drops the frame.
- D. It forwards it out interface G0/2 only.
Answer: B
NEW QUESTION 7
SIMULATION
Configure IPv4 and IPv6 connectivity between two routers. For IPv4, use a /28 network from the 192.168.1.0/24 private range. For IPv6, use the first /64 subnet from the 2001:0db8:aaaa::/48 subnet.
* 1. Using Ethernet0/1 on routers R1 and R2, configure the next usable/28 from the 192.168.1.0/24 range. The network 192.168.1.0/28 is unavailable.
* 2. For the IPv4 /28 subnet, router R1 must be configured with the first usable host address.
* 3. For the IPv4 /28 subnet, router R2 must be configured with the last usable host address.
* 4. For the IPv6 /64 subnet, configure the routers with the IP addressing provided from the topology.
* 5. A ping must work between the routers on the IPv4 and IPv6 address ranges.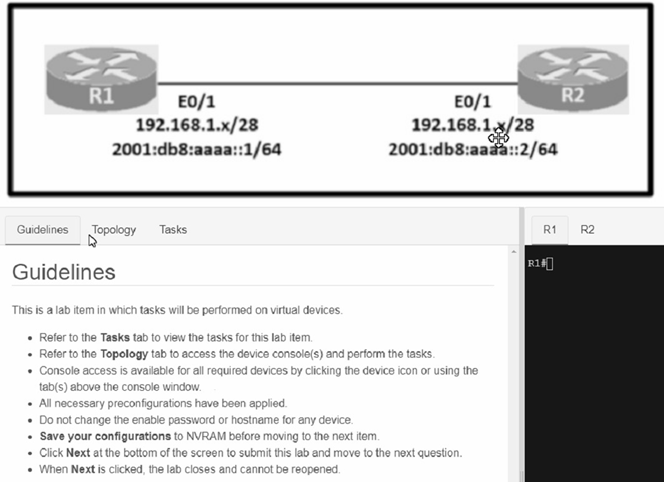
Solution:
Answer as below configuration:
on R1
config terminal
ipv6 unicast-routing inter eth0/1
ip addre 192.168.1.1 255.255.255.240
ipv6 addre 2001:db8:aaaa::1/64 not shut
end
copy running start
on R2
config terminal
ipv6 unicast-routing inter eth0/1
ip address 192.168.1.14 255.255.255.240
ipv6 address 2001:db8:aaaa::2/64 not shut
end
copy running start
---------------------
for test from R1
ping ipv6 2001:db8:aaaa::1
for test from R2
ping ipv6 2001:db8:aaaa::2
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 8
Which virtual MAC address is used by VRRP group 1?
- A. 0050.0c05.ad81
- B. 0007.c061.bc01
- C. 0000.5E00.0101
- D. 0500.3976.6401
Answer: C
Explanation:
The virtual router MAC address associated with a virtual router is an IEEE 802 MAC Address in the following format:
00-00-5E-00-01-{VRID} (in hex in internet standard bit-order)
NEW QUESTION 9
How do traditional campus device management and Cisco DNA Center device management differ in regards to deployment?
- A. Cisco DNA Center device management can deploy a network more quickly thantraditional campus device management
- B. Traditional campus device management allows a network to scale more quickly than with Cisco DNA Center device management
- C. Cisco DNA Center device management can be implemented at a lower cost than most traditional campus device management options
- D. Traditional campus device management schemes can typically deploy patches and updates more quickly than Cisco DNA Center device management
Answer: A
NEW QUESTION 10
DRAG DROP
Drag and drop the DNS commands from the left onto their effects on the right.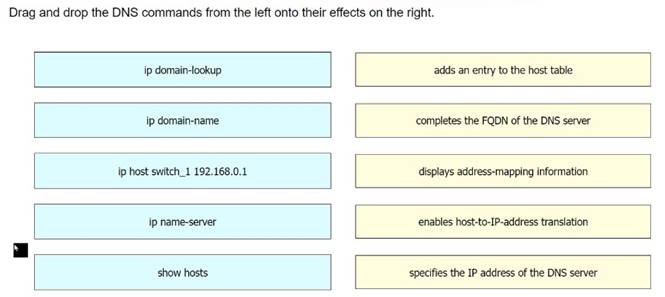
Solution:
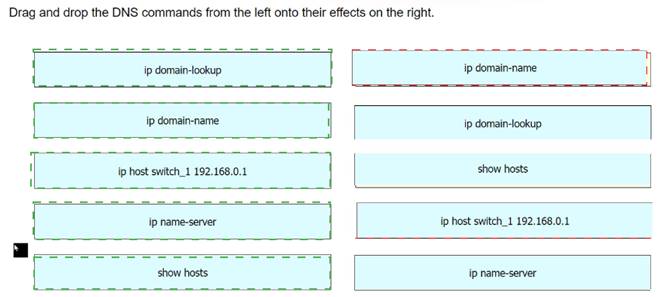
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 11
Refer to the exhibit.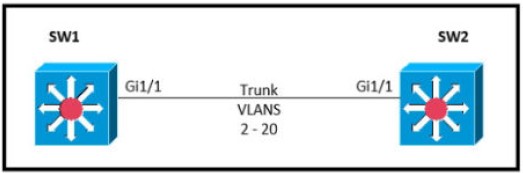
Which command must be executed for Gi1.1 on SW1 to become a trunk port if Gi1/1 on SW2 is configured in desirable or trunk mode?
- A. switchport mode trunk
- B. switchport mode dot1-tunnel
- C. switchport mode dynamic auto
- D. switchport mode dynamic desirable
Answer: C
NEW QUESTION 12
Refer to the exhibit.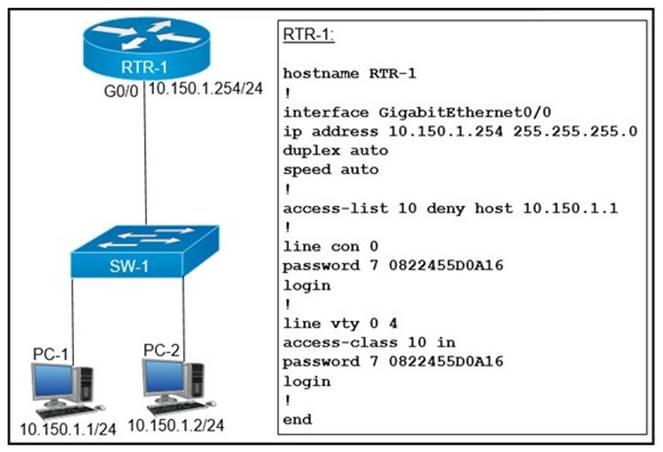
An access list is created to deny Telnet access from host PC-1 to RTR-1 and allow access from all other hosts A Telnet attempt from PC-2 gives this message:"% Connection refused by remote host" Without allowing Telnet access from PC-1, which action must be taken to permit the traffic?
- A. Add the access-list 10 permit any command to the configuration
- B. Remove the access-class 10 in command from line vty 0.4.
- C. Add the ip access-group 10 out command to interface g0/0.
- D. Remove the password command from line vty 0 4.
Answer: A
NEW QUESTION 13
Refer to the exhibit.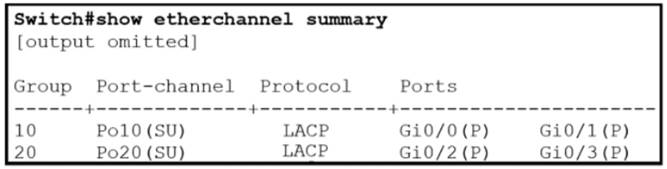
Which two commands were used to create port channel 10? (Choose two )
- A. Option A
- B. Option B
- C. Option C
- D. Option D
- E. Option E
Answer: AC
NEW QUESTION 14
Refer to the exhibit.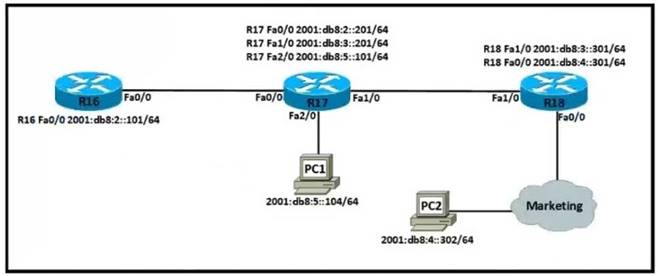
Which IPv6 configuration is required for R17 to successfully ping the WAN interface on R18?
A)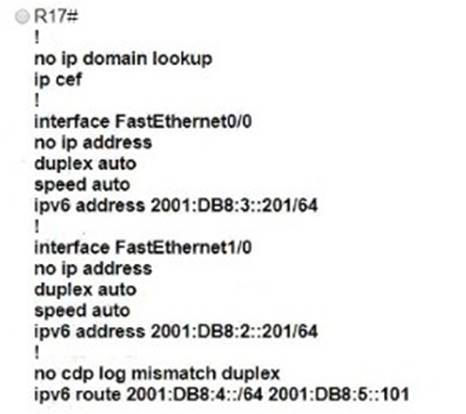
B)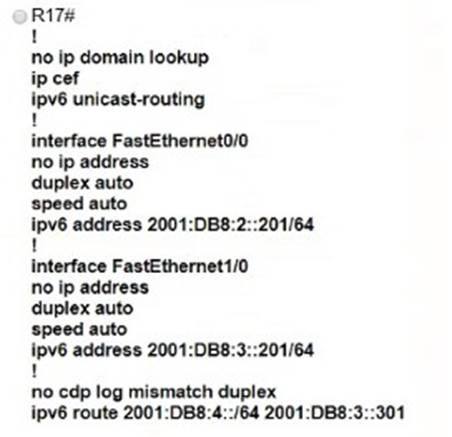
C)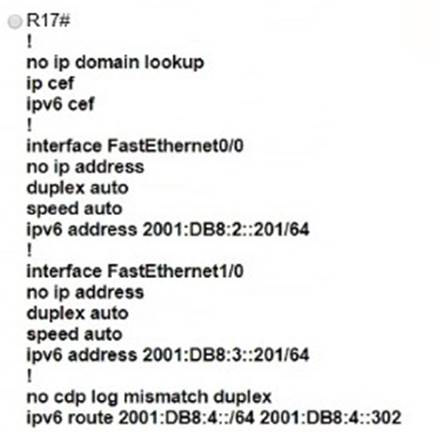
D)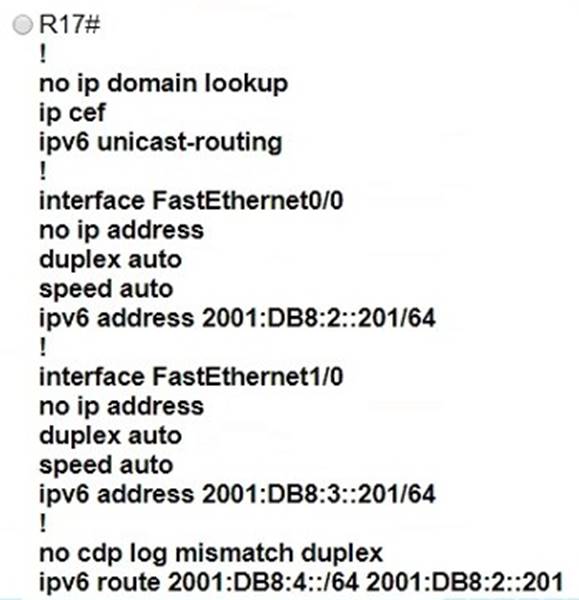
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer: B
Explanation:
ipv6 unicast-routing statement included (IPv6 is enabled on the router).Compared to the exhibit, Fa0/0 and Fa0/1 have correct configurations.The route to subnet 2001:db8:4::/64 points to R18’s Fa1/0 (correct next-hop).
NEW QUESTION 15
What is a characteristic of private IPv4 addressing?
- A. traverse the Internet when an outbound ACL is applied
- B. issued by IANA in conjunction with an autonomous system number
- C. composed of up to 65.536 available addresses
- D. used without tracking or registration
Answer: D
NEW QUESTION 16
DRAG DROP
Drag and drop the descriptions of file-transfer protocols from the left onto the correct protocols on the right.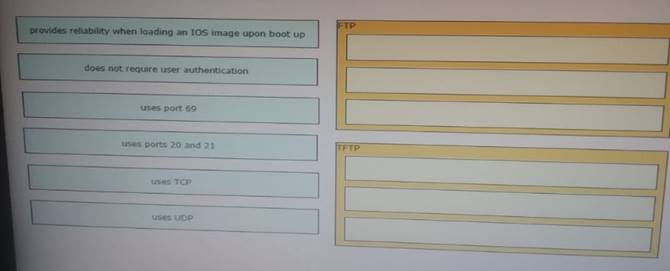
Solution:
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 17
Which type of address is the public IP address of a NAT device?
- A. outside global
- B. outsdwde local
- C. inside global
- D. insride local
- E. outside public
- F. inside public
Answer: C
Explanation:
NAT use four types of addresses:* Inside local address – The IP address assigned to a host on the inside network. The address is usually not an IP address assigned by the Internet Network Information Center (InterNIC) or service provider.This address is likely to be an RFC 1918 private address.* Inside global address – A legitimate IP address assigned by the InterNIC or service provider that represents one or more inside local IP addresses to the outside world.* Outside local address – The IP address of an outside host as it is known to the hosts on the inside network.* Outside global address – The IP address assigned to a host on the outside network. The owner of the host assigns
this address.
NEW QUESTION 18
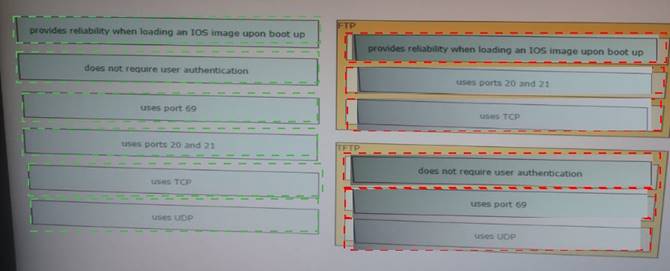
DRAG DROP
Drag and drop the threat-mitigation techniques from the left onto the types of threat or attack they mitigate on the right.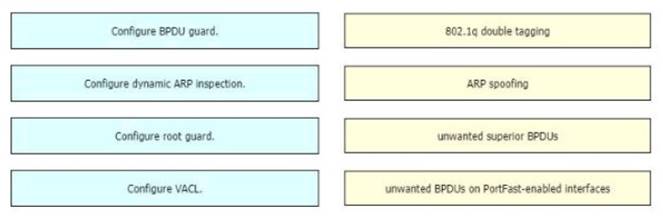
Solution:
Double-Tagging attack:
In this attack, the attacking computer generates frames with two 802.1Q tags. The first tag matches the native VLAN of the trunk port (VLAN 10 in this case), and the second matches the VLAN of a host it wants to attack (VLAN 20).When the packet from the attacker reaches Switch A, Switch A only sees the first VLAN 10 and it matches with its native VLAN 10 so this VLAN tag is removed. Switch A forwards the frame out all links with the same native VLAN 10. Switch B receives the frame with an tag of VLAN 20 so it removes this tag and forwards out to the Victim computer.Note: This attack only works if the trunk (between two switches) has the same native VLAN as the attacker.To mitigate this type of attack, you can use VLAN access control lists (VACLs, which applies to all traffic within a VLAN. We can use VACL to drop attacker traffic to specific victims/servers) or implement Private VLANs.ARP attack (like ARP poisoning/spoofing) is a type of attack in which a malicious actor sends falsified ARP messages over a local area network as ARP allows a gratuitous reply from a host even if an ARP request was not received. This results in the linking of an attacker’s MAC address with the IP address of a legitimate computer or server on the network. This is an attack based on ARP which is at Layer 2.Dynamic ARP inspection (DAI) is a security feature that validates ARP packets in a network which can be used to mitigate this type of attack.
Does this meet the goal?
- A. Yes
- B. Not Mastered
Answer: A
NEW QUESTION 19
What are two characteristics of a small office / home office connection environment? (Choose two.)
- A. It requires 10Gb ports on all uplinks.
- B. It supports between 50 and 100 users.
- C. It supports between 1 and 50 users.
- D. It requires a core, distribution, and access layer architecture.
- E. A router port connects to a broadband connection.
Answer: CE
NEW QUESTION 20
......
100% Valid and Newest Version 200-301 Questions & Answers shared by Allfreedumps.com, Get Full Dumps HERE: https://www.allfreedumps.com/200-301-dumps.html (New 990 Q&As)
- [2021-New] Cisco 640-911 Dumps With Update Exam Questions (31-40)
- [2021-New] Cisco 200-125 Dumps With Update Exam Questions (12-21)
- [2021-New] Cisco 200-310 Dumps With Update Exam Questions (31-40)
- [2021-New] Cisco 300-101 Dumps With Update Exam Questions (13-22)
- [2021-New] Cisco 200-125 Dumps With Update Exam Questions (1-10)
- All About Realistic 200-201 Free Dumps
- [2021-New] Cisco 642-035 Dumps With Update Exam Questions (1-10)
- Realistic Cisco 200-301 Test Questions Online
- [2021-New] Cisco 400-251 Dumps With Update Exam Questions (111-120)
- [2021-New] Cisco 400-101 Dumps With Update Exam Questions (61-70)

